
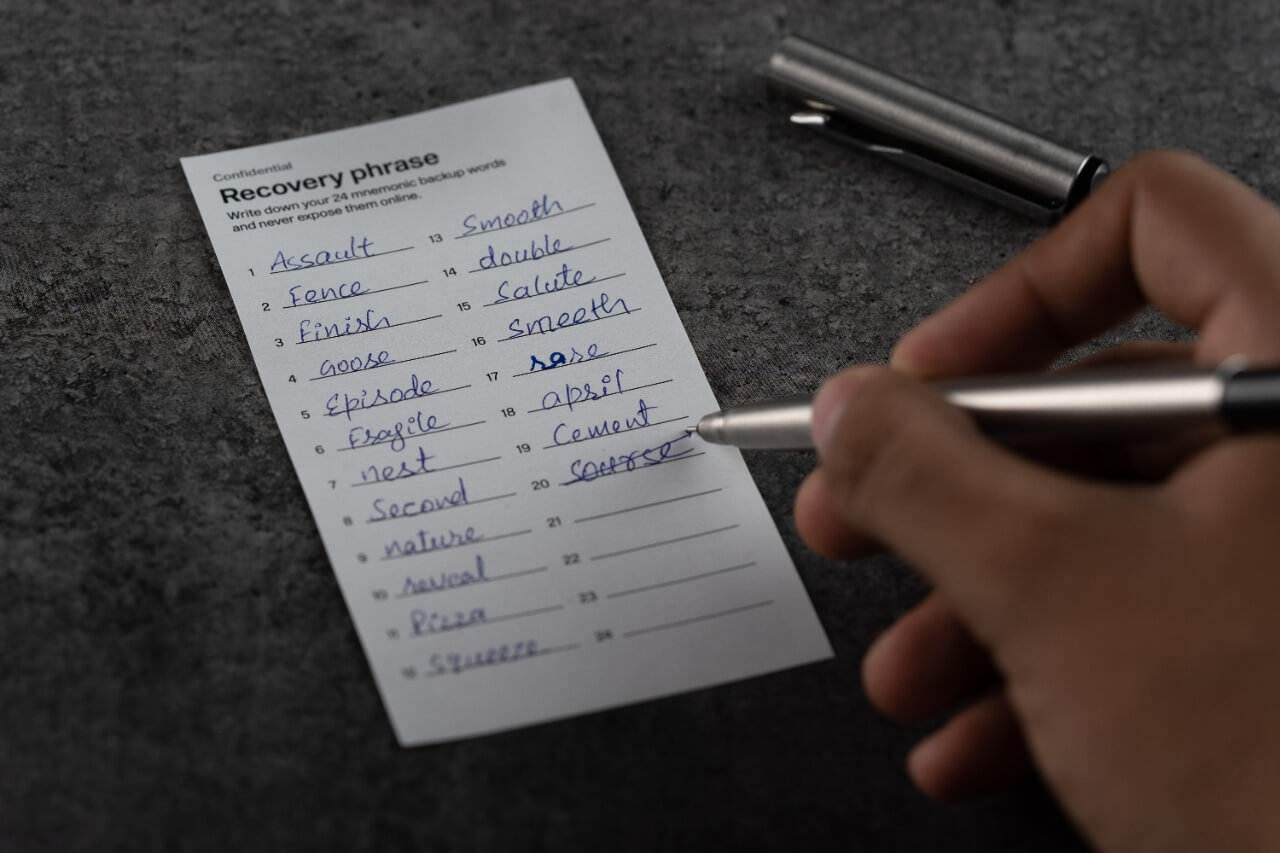
Have you ever wondered what would happen if you lost the recovery phrase to your cryptocurrency wallet? Would your assets be gone forever? This is a common worry for crypto users today. But what if there was a better, safer way to store your crypto without relying on a single recovery seed? That’s where seedless wallets come in.
As a crypto investor, securing your digital assets is one of the most important things you can do. Traditional wallets rely on seed phrases — a set of words that you must write down and store safely — to recover your funds. But what if you lose that seed phrase or worse, someone steals it? Seedless wallets eliminate this problem, offering a more secure and convenient way to manage your crypto. Learning about seedless wallets is crucial for anyone serious about protecting their digital assets, especially as more advanced technologies become available.
In this article, we’re going to explore what seedless wallets are, how they work, and why they’re quickly becoming the future of cryptocurrency security. We’ll also review the different types of seedless wallets, compare some of the most popular ones, and explain why they’re a game-changer for users. Let’s dive in!
A seedless wallet is a type of cryptocurrency wallet that does not require a traditional recovery seed phrase to back up or restore your funds. In most crypto wallets, you are given a set of random words called a seed phrase that you must write down and store securely. This seed phrase is the key to recovering your wallet if you lose access to it. However, seedless wallets eliminate the need for this recovery phrase altogether by using advanced security methods to protect and recover your crypto.
Instead of relying on a single recovery phrase, seedless wallets use other technologies like decentralized key storage or multi-party computation to secure your private keys. In some cases, the private key is broken into multiple pieces and stored across different devices or components, making it nearly impossible for someone to steal or lose access to the full key. This approach adds an extra layer of security and reduces the risk of a single point of failure.
Note: Cypherock X1 is BIP39 compatible, and seedless does not mean Cypherock X1 has no seed phrase. Rather, you are not required to back up the seed phrase if you do not want to.
Traditional wallets store your private keys and use a seed phrase as a backup, but seedless wallets take different approaches to ensure your fund's security. Here’s how it typically works:
Instead of generating a single private key stored in one place, a seedless wallet splits this key into multiple pieces. These pieces are stored across several different devices or locations. For example, one part might be on your phone, another part on a hardware wallet, and a third part in a secure cloud storage. This ensures that no single device or location has the full key, reducing the risk of theft or accidental loss.
One popular method used in seedless wallets is called Shamir Secret Sharing. In this method, your private key is broken into different "shares," and a certain number of shares are needed to reconstruct the key. Even if one share is lost or compromised, as long as you have the required number of remaining shares, you can still recover your wallet. This provides an extra layer of security and flexibility.
Another advanced technique is multi-party computation (MPC). In this approach, several devices work together to authorize a transaction, but none of the devices has access to the entire private key at any point. This way, even if one device is hacked or stolen, your funds remain safe because the full key is never exposed.
Unlike traditional wallets, which require you to write down a 12 or 24-word seed phrase and store it securely, seedless wallets remove this hassle. There’s no single phrase that, if lost, could lock you out of your crypto forever. Instead, the recovery process involves gathering the necessary parts of your decentralized key.
There are several types of seedless wallets available, each offering unique methods for protecting your private keys without relying on traditional seed phrases. These wallets use advanced cryptography and decentralization to provide secure and efficient ways to manage your cryptocurrency. Let’s explore the most common types of seedless wallets:
Multi-component wallets, like the Cypherock X1, divide your private key into multiple parts and store these pieces on separate hardware components. These components work together to authorize transactions, but none of them contains the full private key by itself. This ensures that even if one component is lost or stolen, your funds remain secure as long as the remaining pieces are intact.
MPC wallets, like ZenGo, use multi-party computation technology to distribute key management across multiple devices or parties. Instead of storing a full private key on any single device, different parts of the key are used collectively to sign transactions.
Social recovery wallets are designed to help you recover your funds if you lose access to your wallet. Instead of a recovery seed, these wallets use trusted contacts or devices to help you regain access.
Some wallets store parts of your private key securely in cloud storage as part of a seedless recovery solution. These cloud-based wallets use strong encryption and decentralization to ensure that your key is protected, even if a device is compromised.
Smart contract wallets, such as Argent, use blockchain technology to manage your private keys and enable secure recovery options. These wallets allow users to set up rules, like requiring multiple approvals for transactions or adding "guardians" to help recover access.
Seedless wallets offer enhanced security by eliminating the need for traditional seed phrases, using technologies like decentralized key storage and multi-party computation (MPC). While they simplify recovery and reduce risks, they come with challenges such as more complex setups and reliance on multiple components. Below is a quick comparison of the pros and cons of seedless wallets:
This review highlights top seedless wallets that enhance security without using traditional recovery phrases. We'll compare their key features, benefits, and limitations to help you choose the best option for managing your crypto securely.
Cypherock X1 is a cutting-edge hardware wallet that focuses on decentralized key management. Instead of storing a private key on a single device or generating a seed phrase, it splits the private key across four hardware components using Shamir Secret Sharing. This wallet provides an advanced level of security by ensuring that no single device holds the full key, making it highly resistant to theft or loss.
Img Alt- Cypherock X1 wallet
Pros:
Cons:
ZenGo is a mobile seedless wallet that uses multi-party computation (MPC) technology to secure your private key without requiring a seed phrase. The wallet splits key management between your device and ZenGo’s servers, making it highly secure and easy to recover in case you lose access to your phone. It’s known for its simplicity and user-friendly design.
Img Alt- Zengo wallet
Pros:
Cons:
Argent is a smart contract-based wallet that operates on the Ethereum network, offering seedless recovery through a unique social recovery model. It allows users to designate trusted contacts (called "guardians") to help recover the wallet if access is lost. Argent combines ease of use with the security of decentralized smart contracts, making it a popular choice for Ethereum users.
Img- Argent wallet
Pros:
Cons:
When choosing a seedless wallet, it’s essential to focus on key factors that ensure the safety, usability, and flexibility of your cryptocurrency management. Here’s what to look for in a seedless wallet:
The most crucial aspect of any wallet is its security. Look for wallets that offer advanced protection, such as decentralized key management, multi-party computation (MPC), or Shamir Secret Sharing. These technologies ensure that your private key is split into multiple parts or never fully exposed, minimizing the risk of theft or hacking.
A seedless wallet can be a bit tricky, especially if you're new to cryptocurrency, but it's essential to find one that maintains a balance between ease of use and security. It's important to choose a wallet with a clear and user-friendly interface that guides you through these processes without compromising on security.
Since seedless wallets don’t use a seed phrase for recovery, make sure the wallet has a straightforward recovery method. This might involve trusted contacts (social recovery), hardware components, or cloud-based storage. Make sure you understand how to recover your wallet in case of a lost device or forgotten password.
Some seedless wallets only support specific blockchains, such as Argent for Ethereum. If you hold various types of cryptocurrency, ensure that the wallet supports multiple coins and tokens. Check for compatibility with your portfolio, especially if you want to manage different types of assets in one place.
Always choose a wallet from a reputable company with a track record of providing secure solutions. Check for reviews, customer feedback, and active community support. Wallets like Cypherock X1 and ZenGo have established themselves as trusted options with solid user support.
When choosing a wallet, consider whether a hardware-based option like Cypherock X1 or a software-based wallet like ZenGo is right for you. Hardware wallets offer an additional layer of physical security, keeping your assets offline and protected from digital threats.
While they may not be as instantly accessible as software wallets, which offer convenience and portability on mobile devices, the enhanced security of hardware wallets makes them a strong choice for those who prioritize safeguarding their assets.
The future of wallet security is moving beyond seed phrases, so you no longer have to depend on older methods that come with risks. New technologies like decentralized key storage, multi-party computation (MPC), Shamir Secret Sharing, biometric authentication, and social recovery models offer stronger security and make wallets easier to use. These innovations give you peace of mind, whether you’re new to cryptocurrency or have been investing for some time.
As more people join the crypto space, these advanced seedless wallets will become the new standard. With them, you can store and manage your assets securely, without the stress or hassle of traditional seed-based recovery systems.
When you start investing in cryptocurrency, securing your digital assets should be a top priority. Seedless wallets are becoming the future of crypto security because they remove the risks of traditional seed phrases. If you are ever worried about losing your recovery seed, with a seedless wallet, that's no longer an issue. These wallets use advanced technologies like decentralized key storage, multi-party computation (MPC), and Shamir Secret Sharing to keep your funds safe.
By choosing a seedless wallet, you're not only increasing security but also making crypto management easier. There’s no need to track a single seed phrase, and even if a device is lost, your assets remain protected. Wallets like Cypherock X1, ZenGo, and Argent offer these benefits, giving you peace of mind and control over your investments.
As cryptocurrency adoption grows, seedless wallets will likely become the standard for secure asset management. If you’re serious about protecting your crypto, now’s the time to consider switching to a seedless wallet. You'll get stronger security and simpler recovery options, letting you focus on growing your portfolio without worrying about losing access to your funds.
The best type of wallet depends on your needs. Hardware wallets, like Cypherock X1, offer the highest security by keeping your private keys offline and distributed. Seedless wallets provide convenience without relying on seed phrases, while software wallets are easier to access on mobile devices but might be less secure than hardware options.
A seed phrase is a sequence of 12 to 24 randomly generated words that serve as a backup to restore access to a cryptocurrency wallet. If you lose your wallet or device, you can use this phrase to recover your funds.
The 24 words, also known as a seed phrase or recovery phrase, are a set of randomly generated words that act as the master key to your crypto wallet. These words allow you to restore your wallet on another device if needed, and losing them could result in losing access to your assets.
Start securing your crypto journey today—visit Cypherock X1 to learn more.
Connect with us:
Twitter: @CypherockWallet
Telegram: Join the Community
