

Everyone is familiar with the term HODL in the crypto space, but what is the right way to do it securely? There are different HODLing techniques that have evolved over the last 10 years, each different from the other in terms of technical acumen requirements, ease of accessibility and the security of the funds.
Though both accessibility and security are important factors, there always tends to be a trade off between both. It is up to you as a user to decide, what works for you the best. We will try to list down the most commonly used ones and address the problems with each.
Based on observation, some striking similarities can be drawn out between storage of physical assets like cash and gold and Blockchain based digital assets today. The common behaviour of keeping physical assets in a secure storage vault can be observed as a practice being followed for securing digital assets too. In fact, that is what the current hardware wallets enable, but they face the same single point of failure problem (data loss or data theft) that physical assets face.
A hardware wallet is a great solution if you have to protect small to medium amount of your portfolio and need to use those funds relatively frequently. But the current generation of hardware wallets does not provide a complete cryptocurrency storage and security solution, since the user needs to put a stronger emphasis on protecting their recovery phrases as these are always left exposed in plain text. The seed phrase/recovery phrase is generally written on a piece of paper which opens the same set of problems with paper wallets that hardware wallets initially intended to solve. For a more thorough understanding of the problems, we would recommend checking out our other blog.
One solution for protecting the seed phrase has been to use metal sheets and engrave the seed words on it. This is considered a safe and durable way to store the words but there has been proof that it doesn’t work sometimes. Apart from metal sheets not being durable and having a single point of failure, storing the most crucial seed phrase information in plain text defeats the whole purpose of securing it safely. Choosing to encrypt the seed phrase before storing them on the metal plate is also not effective, as the user has to now secure the encryption key instead.
The best way to protect the seed phrase is to use a Shamir Secret Sharing algorithm. This method has 3 benefits-
i. The seed phrase is completely encrypted and split into multiple shares.
ii. The original seed phrase can’t be reconstructed without a minimum threshold of shares thus preventing a single-point-of-failure.
iii. Effectively tackles the $5 wrench problem.
We believe that everyone has the freedom to choose their crypto community and everyone has the choice to create their own blockchains if they want. Moreover, crypto is about freedom of choice. So instead of solving the HODL issue with single-sig & multi-sig, it is better to create a tamper-resistant off-chain solution to keep the information offline, which is somewhat similar to multi-sig, but can support all the digital assets and at the same time does not have a single point of storage like single-sig.

Fig. Asset Distribution
For securing the physical assets, the best method people resort to today is asset distribution, i.e, storing assets in remote locations to reduce the risk of losing those assets. This leads us back to the question — “how to secure cryptocurrency safely and reliably?” . The answer to this lies in
ensuring a single-point-of-failure doesn’t exist while storing the private keys.
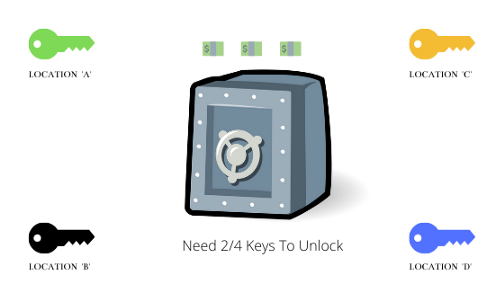
Fig. Access Distribution
So, instead of asset distribution what if we did access distribution? That would mean the assets remain at a single location but, to access it, you would need multiple access points. This is somewhat not feasible with physical assets since they need to be stored in a single location, but definitely possible with digital assets since they are intangible in nature. This makes distributing the access keys to digital assets an optimal solution to prevent a single point of attack. As far as Blockchain based assets are concerned, access distribution is possible through Multi-sig or Shamir Secret Sharing.
So now that we have discussed about various techniques that can be used to HODL cryptocurrencies, it is important to focus on some essential practices to ensure the security of the funds irrespective of the technique you prefer. Here are some important steps that can be considered to ensure a safe HODL experience:
Many HODLers usually operate with a watch-only address and send all their long-term investments to this address. In such situations, the private keys are not used often since the address is accessed only rarely.
At Cypherock, Shamir Secret Sharing Scheme is used in Cypherock X1 to create cryptographic shares to ensure that the private keys of a wallet is split among different tamper-resistant hardware to have an effective mechanism for wallet recovery and fund storage. You can geographically distribute the X1 cards which have encrypted shares or give them to a trusted set of people without worrying about getting hacked or losing their funds since each card has PIN protection just like your hardware wallets. Any 1 out of the 4 X1 cards along with the X1 wallet are needed to recover the funds. The seed phrase is hence protected through access distribution rather than the traditional asset distribution.
If you are someone who prefers a single-sig wallet like a hardware wallet for HODLing, Cypherock X1 will be useful to secure the seed phrase of the wallet. Infact, it can secure multiple seed phrase of different wallets in a single product. But if you are someone who wants similar security properties of a multi-sig wallet but find multi-sig daunting or if multi-sig does not support the Blockchain asset that you want, then Cypherock X1 can be used to secure the assets with similar security properties of an onchain multi-sig.
It intends to solve the key management problems with cryptocurrencies and wants users to have the same peace of mind and confidence in holding their own Crypto that they have (*assume to have) with their fiat money in the banks.

We are live for pre orders @ Cypherock.com
Connect with us:
